- cobalt strike 4
- evasion 4
- injection 4
- redteam 4
- python 3
- pyramid 2
- BOF 1
- assembler 1
- backdoor 1
- coff 1
- module overloading 1
- module stomping 1
- process stomping 1
- reverse-engineering 1
- sRDI 1
- shellcode 1
cobalt strike
Mockingjay revisisted - Process stomping and loading beacon with sRDI
Executables with RWX sections can be abused using a variation of a Process Overwriting technique dubbed Process Stomping. Using (a modified) sRDI and leveraging the new features of Cobalt Strike 4.9 has been possible to load beacon in the RWX section itself without the need for a custom UDRL.
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
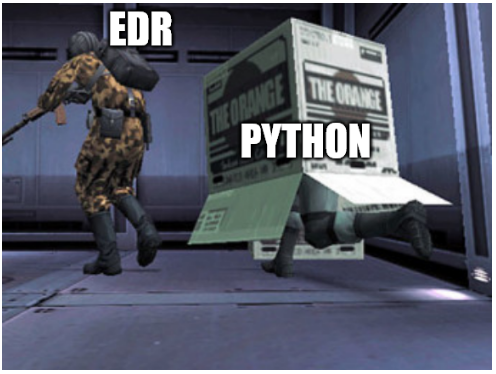
Living-Off-the-Blindspot - Operating into EDRs’ blindspot
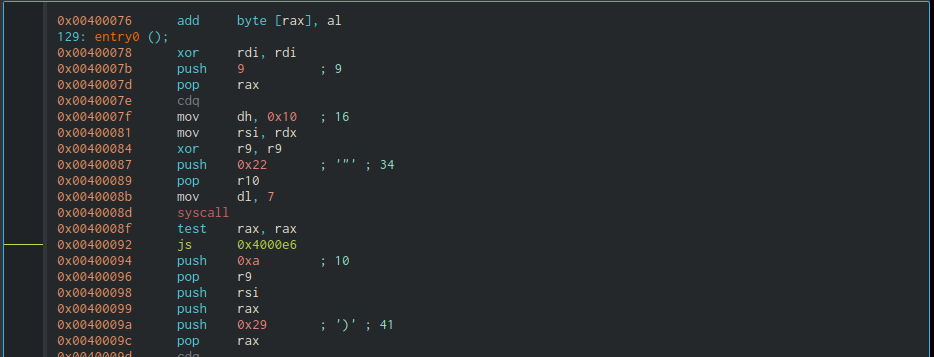
Running Cobalt Strike BOFs from Python
evasion
Raising Beacons without UDRLs and Teaching them How to Sleep
UDRLs and prepended loaders aren’t the only way to execute a raw payload and get a direct hooking in place. In the case of Cobalt Strike, a generic PE loader can be tweaked to execute an UDRL-less Beacon and get direct hooking for an easier prototyping of Sleep obfuscation techniques. Using this approach, two techniques that bypasses the Elastic’s RX -> RW Sleep detection, along with few other scanners, are then demonstrated.
Mockingjay revisisted - Process stomping and loading beacon with sRDI
Executables with RWX sections can be abused using a variation of a Process Overwriting technique dubbed Process Stomping. Using (a modified) sRDI and leveraging the new features of Cobalt Strike 4.9 has been possible to load beacon in the RWX section itself without the need for a custom UDRL.
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
Living-Off-the-Blindspot - Operating into EDRs’ blindspot
injection
Raising Beacons without UDRLs and Teaching them How to Sleep
UDRLs and prepended loaders aren’t the only way to execute a raw payload and get a direct hooking in place. In the case of Cobalt Strike, a generic PE loader can be tweaked to execute an UDRL-less Beacon and get direct hooking for an easier prototyping of Sleep obfuscation techniques. Using this approach, two techniques that bypasses the Elastic’s RX -> RW Sleep detection, along with few other scanners, are then demonstrated.
Mockingjay revisisted - Process stomping and loading beacon with sRDI
Executables with RWX sections can be abused using a variation of a Process Overwriting technique dubbed Process Stomping. Using (a modified) sRDI and leveraging the new features of Cobalt Strike 4.9 has been possible to load beacon in the RWX section itself without the need for a custom UDRL.
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
Running Cobalt Strike BOFs from Python
redteam
Raising Beacons without UDRLs and Teaching them How to Sleep
UDRLs and prepended loaders aren’t the only way to execute a raw payload and get a direct hooking in place. In the case of Cobalt Strike, a generic PE loader can be tweaked to execute an UDRL-less Beacon and get direct hooking for an easier prototyping of Sleep obfuscation techniques. Using this approach, two techniques that bypasses the Elastic’s RX -> RW Sleep detection, along with few other scanners, are then demonstrated.
Mockingjay revisisted - Process stomping and loading beacon with sRDI
Executables with RWX sections can be abused using a variation of a Process Overwriting technique dubbed Process Stomping. Using (a modified) sRDI and leveraging the new features of Cobalt Strike 4.9 has been possible to load beacon in the RWX section itself without the need for a custom UDRL.
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
Living-Off-the-Blindspot - Operating into EDRs’ blindspot
python
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
Living-Off-the-Blindspot - Operating into EDRs’ blindspot
Running Cobalt Strike BOFs from Python
pyramid
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
Living-Off-the-Blindspot - Operating into EDRs’ blindspot
BOF
Back to Top ↑assembler
Back to Top ↑backdoor
Back to Top ↑coff
Back to Top ↑module overloading
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
module stomping
Improving the stealthiness of memory injections techniques
A journey in improving Module Stomping and Module Overloading injection technique, ending up evading Moneta and PE-Sieve
process stomping
Mockingjay revisisted - Process stomping and loading beacon with sRDI
Executables with RWX sections can be abused using a variation of a Process Overwriting technique dubbed Process Stomping. Using (a modified) sRDI and leveraging the new features of Cobalt Strike 4.9 has been possible to load beacon in the RWX section itself without the need for a custom UDRL.
reverse-engineering
Back to Top ↑sRDI
Mockingjay revisisted - Process stomping and loading beacon with sRDI
Executables with RWX sections can be abused using a variation of a Process Overwriting technique dubbed Process Stomping. Using (a modified) sRDI and leveraging the new features of Cobalt Strike 4.9 has been possible to load beacon in the RWX section itself without the need for a custom UDRL.